Cybersecurity Consulting
Managed Service Providers: What to Expect In an MSP Partner
March 02, 2023
6 minutes

The MSP market has grown substantially in the last 10 years as organizations outsource their operational needs. This is because businesses continue to enjoy the benefits of working with a managed service provider partner such as cost-savings and expert support that they can’t get from any other type of company.
The MSP partner market is expected to have an annual growth rate of 13.6% from 2023 to 2030. Because managed services can maximize budgets and reduce the need to hire in-house professionals, organizations continue to rely on their services.
Organizations are investing more in MSPs not just for their IT but also for things like marketing and cybersecurity.
Sign up for our newsletter !
When a managed service provider partner safeguards a business’ network environment, they are labeled an MSSP (managed security service provider).
If you’d first like to learn about DOT Security, an MSSP powered by experts, check out our page Why DOT?
What Do MSPs Offer?
- Flexible models
- Expert consultants
- Access to a large and varied team of IT staff
- Fixed-fee contracts
- Ongoing support
Managed services provide millions of companies in the United States the crucial services they need to function in today’s business world. MSSPs can help shield an organization, especially as cybersecurity threats rise while the sector faces a talent shortage.
Whether a managed service provider partner offers digital marketing, IT management and infrastructure, guidance on digital transformation efforts, or cybersecurity measures; it can help a business reach its goals without having to procure in-house teams.
It’s simply not feasible for most SMBs to hire an internal IT team, and internal marketing team, an internal cybersecurity team, and any other number of departments they might need to fund.
So, instead they turn to MSPs to help fill in the gaps.

Related Blog: 5 Qualities of a Reliable Cybersecurity Company
What Should You Expect from a Managed Service Provider Partner?
If you aren’t familiar with how the managed services model works, it can be hard to define what to expect from an MSP.
Not all MSPs are created equal, and not all will deliver what we would consider to be an acceptable arrangement in a partnership.
When it comes to managed cybersecurity, you should expect the following:
A Thorough Cybersecurity Risk Audit
Every managed security service partnership should start with an in-depth cybersecurity risk assessment that examines the client’s business fully. It allows the service provider to understand what solutions and practices need to be implemented to keep the organization safe.
Be wary of businesses offering free risk audits—these are often not thorough and comprehensive enough to get a full understanding of your whole network environment.
The risk audit should involve complete penetration testing and vulnerability scanning of your network and systems by cybersecurity engineers and analysts.
They can then give you a report of their findings and suggestions on how to move forward.
Full Tech Stack
An MSSP should be able to offer a cybersecurity tech stack tailored to your business needs, comprised of solutions that are appropriate to your organization.
This should include perimeter security, endpoint protection, information security, backup and disaster recovery, network monitoring, and employee cybersecurity training.
This is what is referred to as a layered approach to cybersecurity—businesses today should not be relying on just one or two security solutions. A reliable service provider will offer a comprehensive set of solutions for their clients.
Ongoing Network Monitoring
Once the tech stack has been implemented, a cybersecurity partner should not be “setting and forgetting”.
79% of reporting organizations encountered ransomware attacks. This increase in attacks and the ongoing changes in the cyber threat landscape means proactive network monitoring is a must to avoid data breaches or data loss.
A partner is responsible for correctly and effectively monitoring your network, ensuring threats are contained and that all systems are running as expected, and immediately responding to irregularities if necessary.
The client organization should be assigned a virtual Chief Information Officer (vCIO) for this purpose.
They act as a point of contact and should be monitoring the client’s network at all times and preventing malicious threats.
To do this, they will use the implemented cybersecurity solutions and proactively monitor the network; aggregating, indexing, and analyzing data in order to detect behavioral inconsistencies and protect IT infrastructure.
Ongoing Consultation
Additionally, the vCIO should act as a technology consultant for the organization.
As with any other aspect of business technology, available software and organizational goals change rapidly. Companies need to have someone who’s got their finger on the pulse of where the business is with regards to their security tech.
As your business scales and more employees are onboarded, more devices are added and your systems evolve. A cybersecurity service provider can ensure your security strategy changes with you.
Compliance regulations also change as customer privacy rules get developed or amended. The right MSP partner can ensure your processes safeguard any protected information so you are up to date on compliance requirements.
There are many different factors which can mean a cybersecurity strategy needs to be updated and adjusted. That’s where a business can expect their MSSP to step up with vCIO IT and cybersecurity consulting services on an ongoing, long-term basis.
Related Blog: What is the Role of a vCISO in Cybersecurity?
What Kind of Service Should You Expect From an MSSP?
Is Your MSSP Committed to You?
As with any digital transformation project, cybersecurity is complex and requires true commitment in a partnership.
Security strategies should be planned with a long-term goal and perspective in mind, which you only get from fully understanding the client’s needs on an ongoing basis.
Your MSP partner should take the initiative and play a key role in positioning themselves at the heart of your IT operations—as an extension of the company and not just an outsourced solution provider.
They should provide testing, reporting, implementing, maintaining, and monitoring the solutions necessary to protect your organization, and as such there should be a strong emphasis on ensuring communication between both parties is strong and effective.
The point of contact—vCIO—should consult and maintain a relationship with the partner on a basis that’s suitable for both; whether this is monthly, quarterly, or on any other cadence.
This consistency in reporting and consultation builds trust and helps both parties understand where they’re at and where they need to be for the security strategy to truly succeed.
Certification, Accreditation, and Reputation
What kind of accreditation does your security partner have?
The MSP you choose as your business security partner is who you’re trusting to keep your most prized possession protected. Making sure the vCIO you are given and the company they represent are qualified for the job is essential.
Consider factors like their Net Promoter Score (NPS) to get an understanding of how well they deal with their current client base and check to see what qualifications and certifications their staff have in working with the solutions they implement.
Some MSP cybersecurity partners will have a roster of seasoned cybersecurity veterans, while others will be little more than salespeople.
A Cost Structure that Suits You
The cost structure is one of the key reasons SMBs choose to partner with service providers.
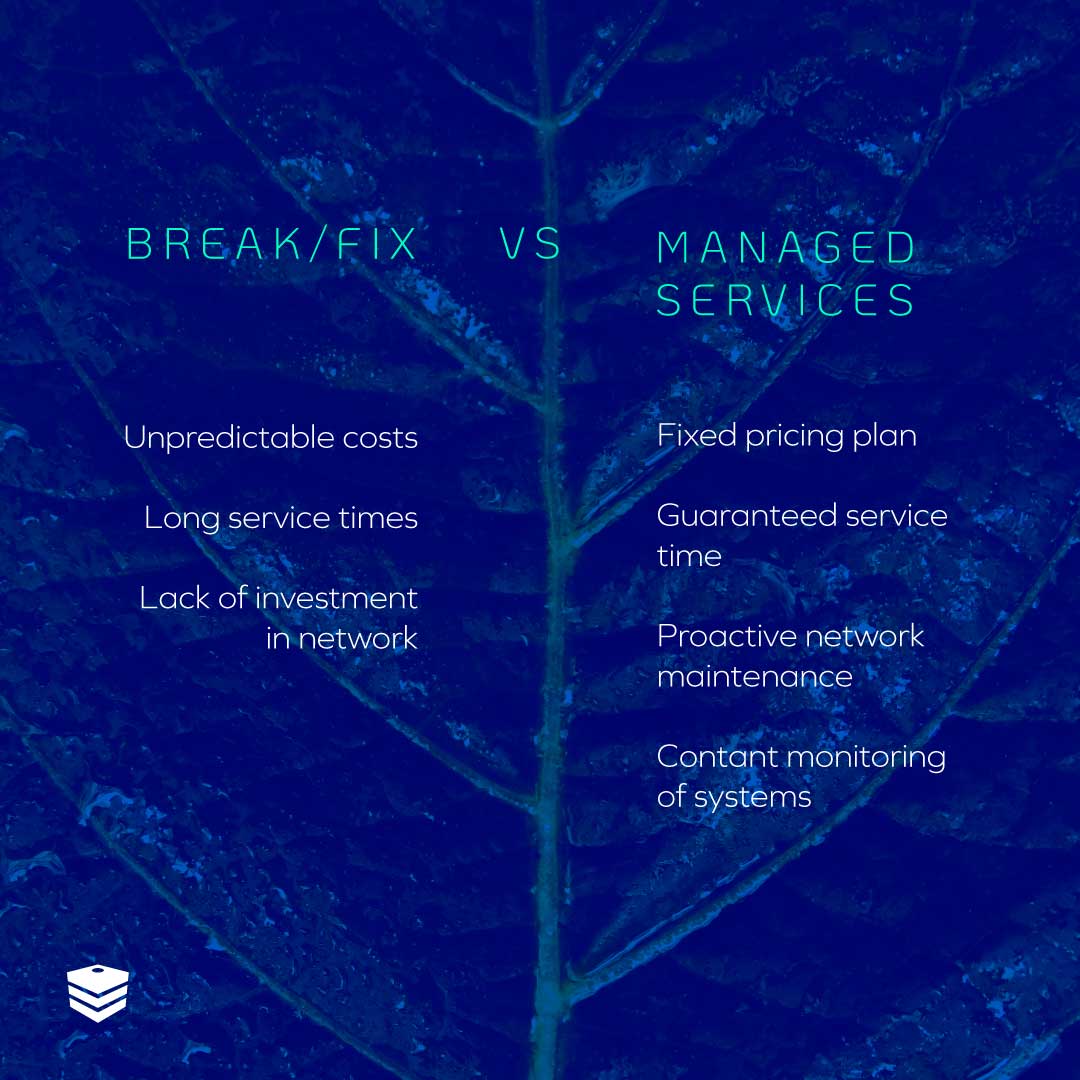
Traditionally, the break-fix model has been common in IT, whereby services are contracted when needed after things break, and are usually billed by the hour. This model is expensive and difficult to budget for.
Many managed service providers, however, offer their expertise as an all-inclusive package.
This means that once a service agreement has been signed, there shouldn’t be any unexpected fees charged in addition to the monthly contract expense.
When partnering with an MSP, make sure the contract suits your needs—most businesses and MSPs are favoring the fixed-fee model today because of its simplicity and attractiveness to SMBs.
Onboarding
Onboarding is an important part of any partnership with a service provider and should be handled properly.
Once the risk assessment has been conducted, the recommendations made, and the contract signed, there should be a timeline put in place for the implementation phase of the agreement.
This means that the strategy going forward for technology adoption is laid out clearly so that both parties have a clear understanding of mutual expectations.
Flexibility and Scalability
Is what the provider is offering flexible and scalable?
As technology environments evolve, business needs evolve too, and this often means that expectations and strategies have to be altered down the line.
If, for example, new solutions that were not in the original agreement must be implemented to comply with new data security regulations, the business needs to know that the MSP partner offers the necessary flexibility to fulfill this new service.
Ensure that the service provider is comfortable being flexible in their approach to service agreements and that they offer scalability when changes need to be made.
A cybersecurity strategy that needs updating should be spotted by the vCIO, who can then make the appropriate recommendations that can then be agreed upon and implemented as necessary, but a flexible and scalable service is necessary to achieve this.
In Conclusion
Partnering with an MSSP can give business leaders peace of mind knowing experts are proactively monitoring their network to detect and stop threats.
Businesses should expect a reliable service provider to have top-of-the-line tools, experienced and passionate experts, and willingness to create a custom security program for each business.
DOT Security offers the expertise, technology, and process to continuously protect our clients. To learn more about why you should partner with DOT Security, check out our page, Why DOT?
